Member
- Joined
- Oct 11, 2023
- Messages
- 105
- Thread Author
- #1
Greetings, friends. Not so long ago, attackers started placing malicious packages in the PyPI repository, disguising various malicious programs as legal components. This campaign has not yet been stopped, and the number of affected developers is currently unknown for sure.
This was not the end of it, the attack on PyPI gave rise to a new meta among the attackers, and this time the public NPM repository was affected.

NPM is a standard package manager that is automatically installed along with Node.js. It is used to download packages from the npm cloud server, or to upload packages to these servers.
However, the methodology of this campaign is slightly different from what we saw earlier: no one uploaded viruses directly to NPM, attackers took advantage of the high reputation of open source sources in search engines and promoted malicious sites, as well as utilities with malicious stuffing through this repository.
There are several vectors of attacks using NPM:
A DoS attack is a hacker attack on a computer system in order to bring it to failure, that is, creating conditions under which bona fide users of the system will not be able to access the provided system resources (servers), or this access will be difficult.
According to a report from Checkmarx, several hackers may be behind this campaign and their ultimate goal is to spread malware such as RedLine Stealer (80%), Glupteba (12%), Smoke Loader (5%) and XMRig (2%).
Redline is particularly dangerous due to a sharp increase in the number of infections, so today we will analyze and analyze it.
RedLine Stealer can steal the following information: usernames, passwords, autofill data, cookies, and credit card information from all web browsers. Cybercriminals can misuse this information to access various accounts (for example, social networks, email, bank accounts, cryptocurrency wallets).
The list of e-wallets targeted by the RedLine hijacker includes Armory, AtomicWallet, BitcoinCore, Bytecoin, DashCore, Electrum, Ethereum, LitecoinCore, Monero, Exodus, Zcash, and Jaxx. The target VPN clients are ProtonVPN, OpenVPN, and NordVPN.
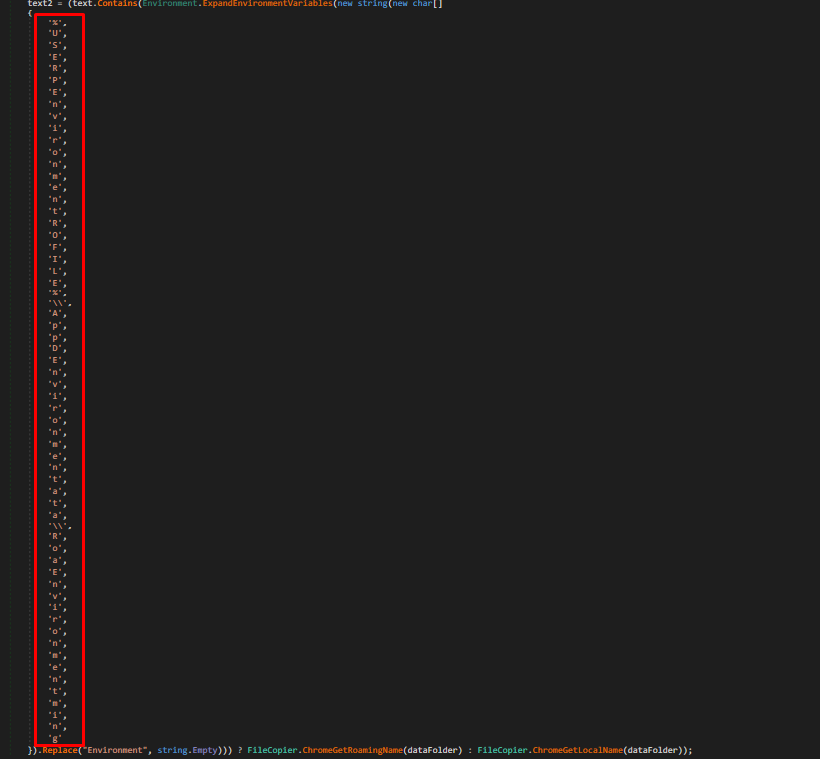
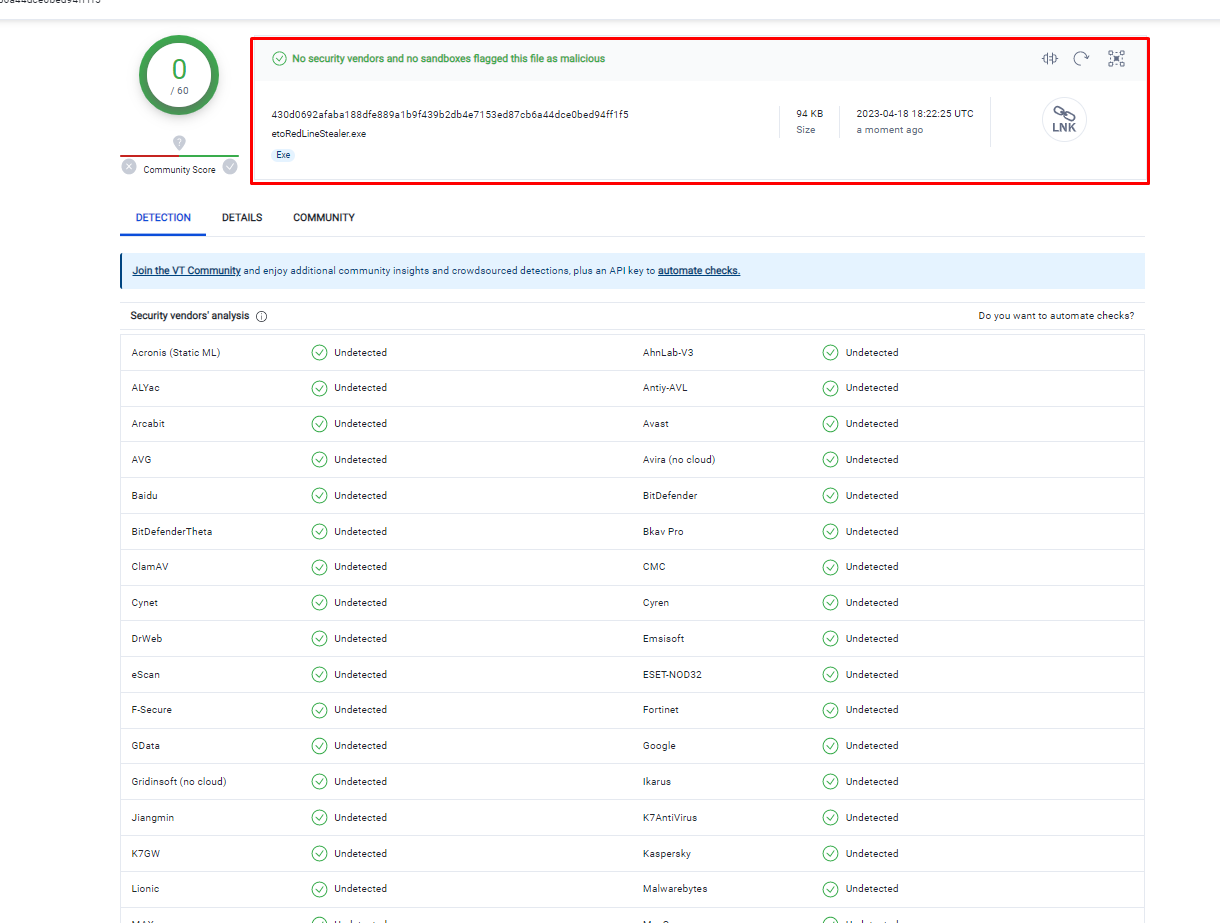
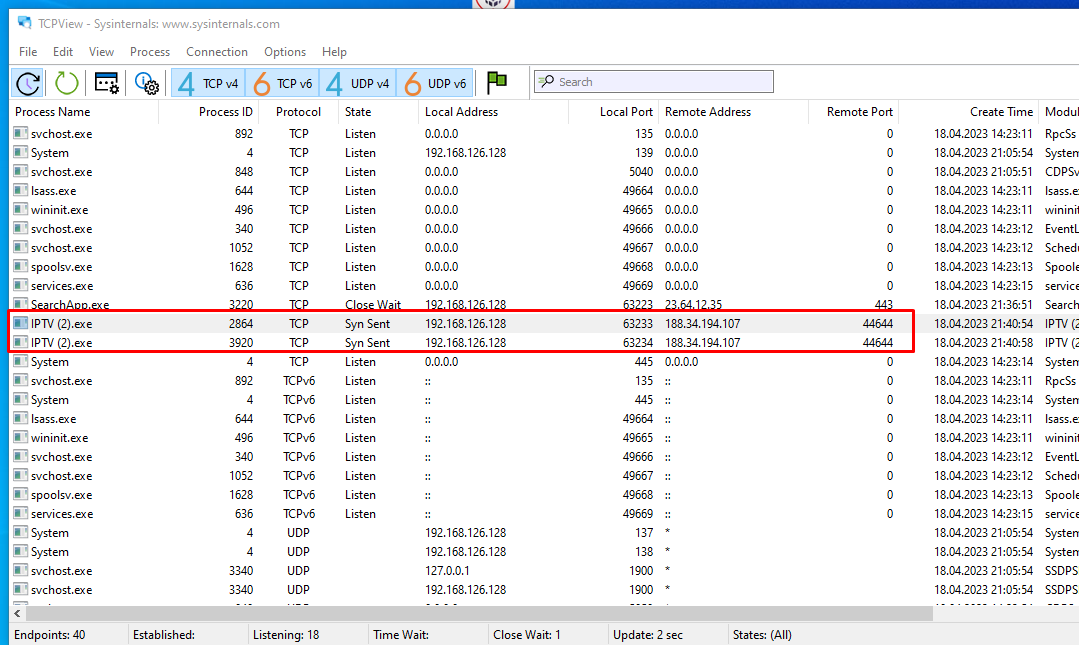
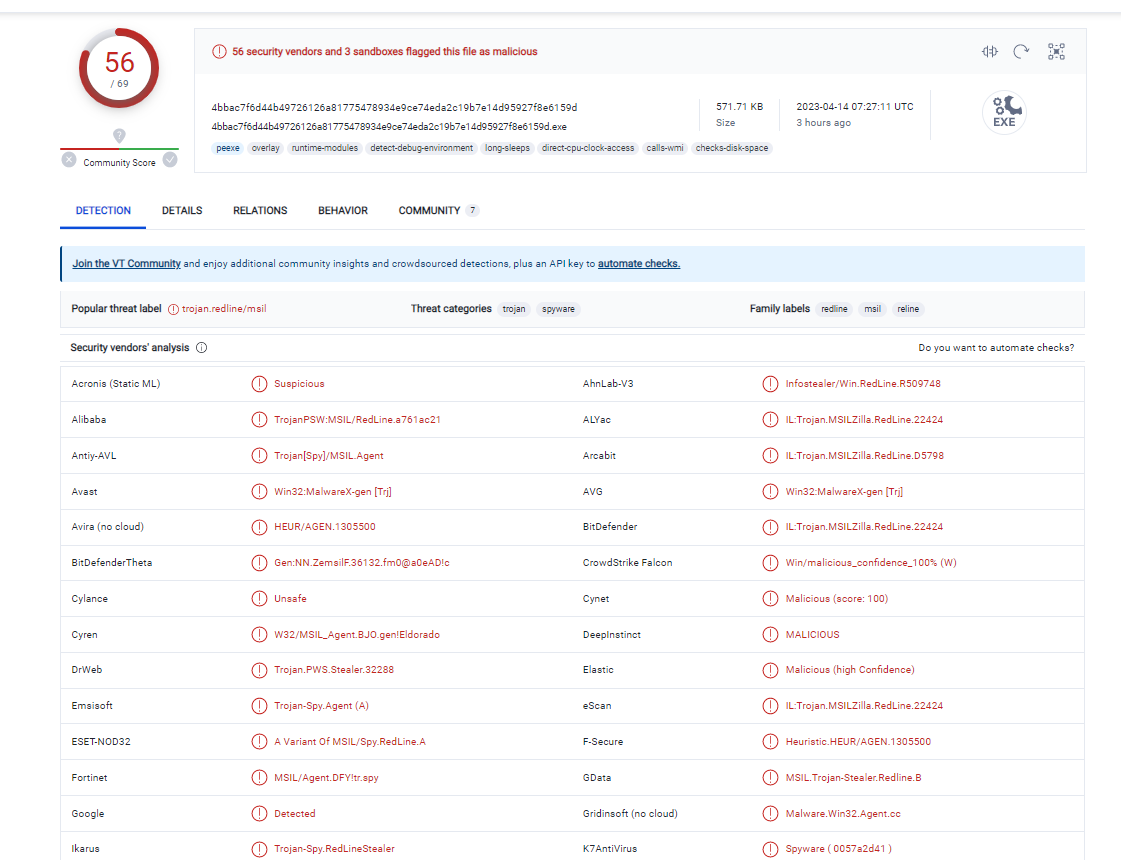
For analysis, we will use a sample dated April 14, 2023. On VirusTotal, it looks like this:
As you can see, there are no problems with detection here, which is good news. The external sample has an IPTV application icon and is presented as an SFX archive, but there is no other information. Let's move on to the analysis.
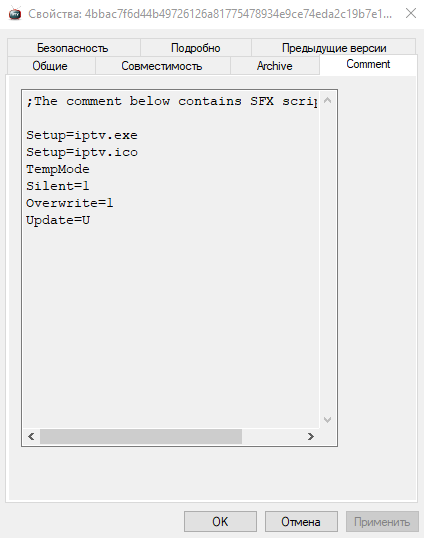
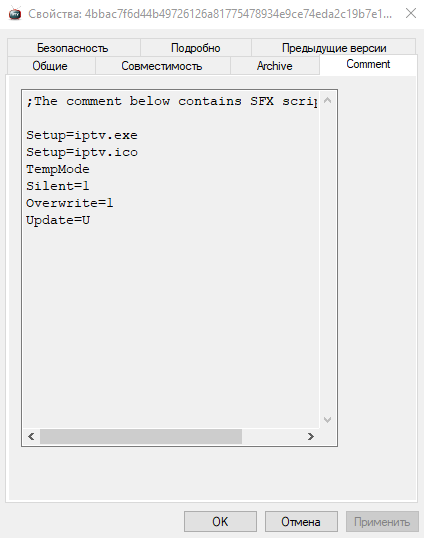
And as mentioned earlier, this is our SFX archive. I would not say that this method of packaging malware is something new and revolutionary. Similarly, in my school years, I packaged a variety of BAT files to make them look like executable. exe files.
A self-extracting or self-extracting archive (SFX) is a file or computer program that combines an archive and executable code for unpacking it. Such archives, unlike regular ones, do not require a separate program to unpack them, if the executable code can be executed in the specified operating system.
In principle, if it were launched now, the content would end up in the AppData folder, where a normal user would hardly find it. But we'll make things a little easier by simply opening .sfx using the archiver. Let's extract the file we are interested in and start parsing it.
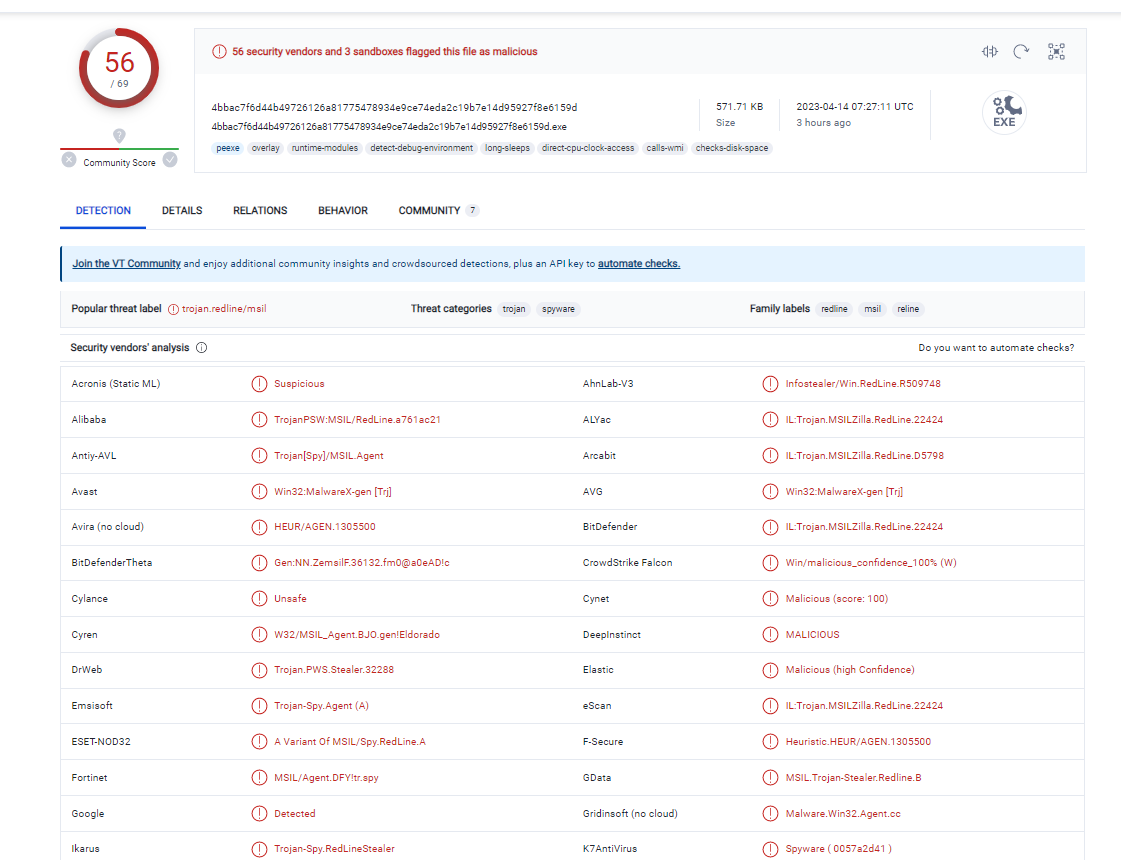
IPTV.exe — this is the name of the extracted file, but it is much more interesting that even when viewing the properties, we can get some useful information, namely:
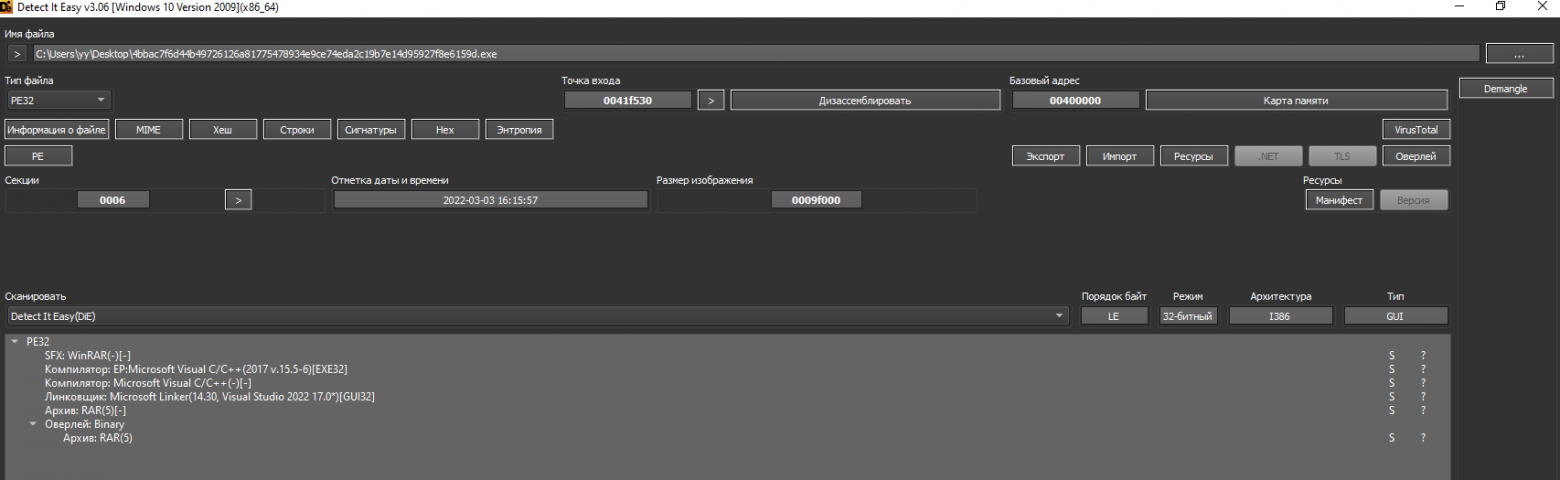
Approximate time of last modification, which is unlikely to be replaced, and the original file name — implossions.exe. When we try to search for this name through the search engine, we immediately see that it belongs to our stiller. The resulting sample weighs 95 KB. Let's go back to DIE for more information about the writing language and compiler of this miracle.
The exact date of creation is unknown, what we see is "Timestomping", and it is an anti-criminalistic method used to mislead the investigation and rapid response specialists.
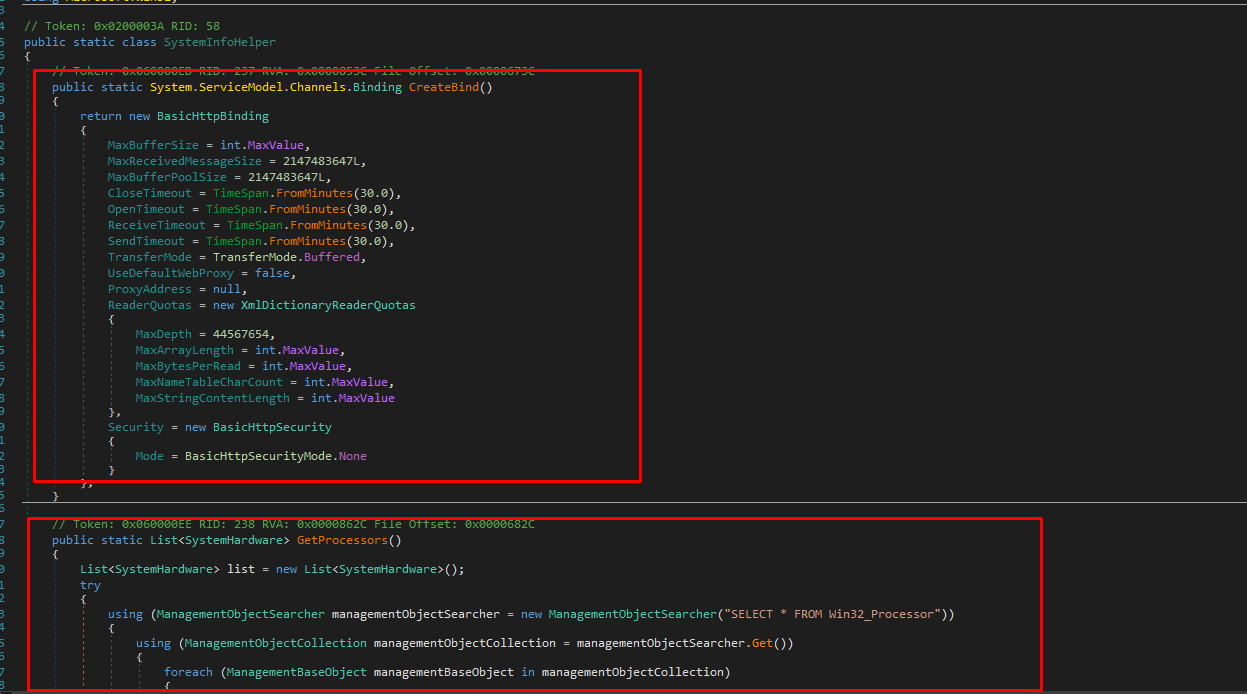
We also see that the malware is a library .NET, and Microsoft Linker was used as the compiler.
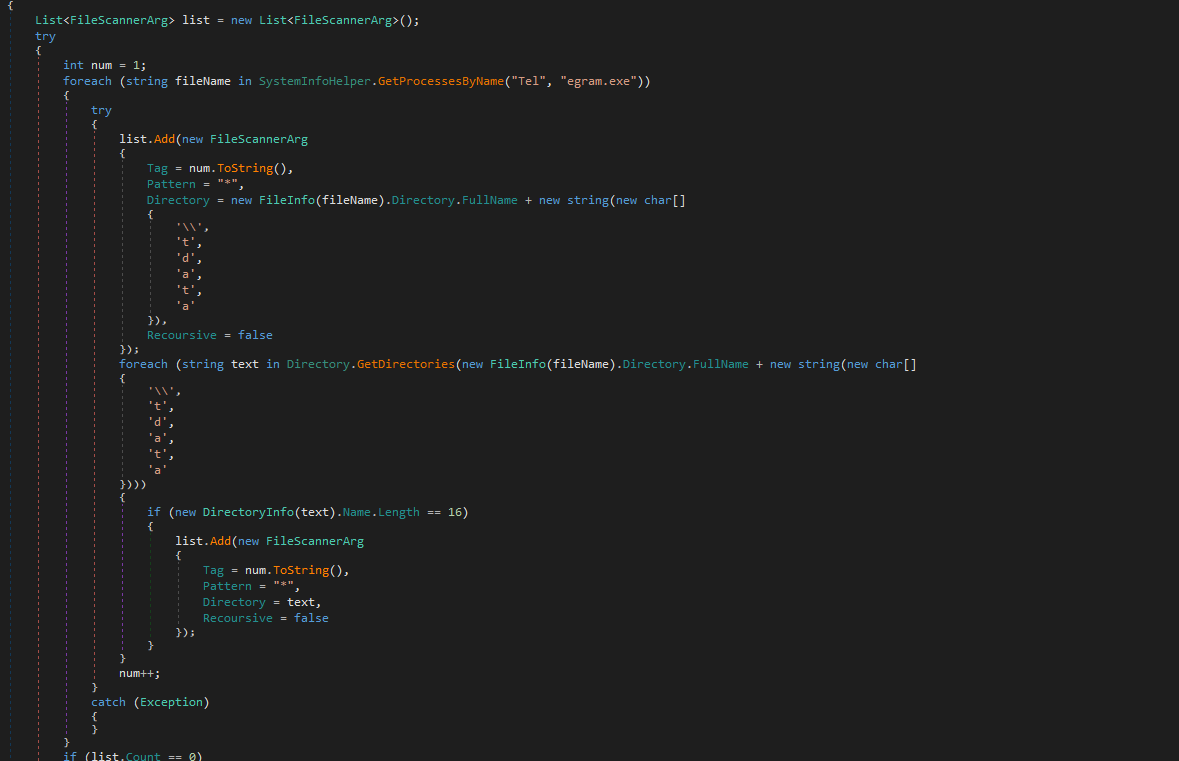
Libraries .NET — in essence, they are the end result of compiling code in C#. Fortunately, we can easily decompile this sample using the dnSpy utility and analyze the clean source code, or at least something close to it. But if I were you, I wouldn't be happy about this, since such accessibility of the code can provoke the appearance of modifications from other attackers, and this already smacks of a full-fledged epidemic.
But first, let's use Tiny Tracer with advanced settings to clearly see what functions stiller uses. This will also display the malware's action plan.
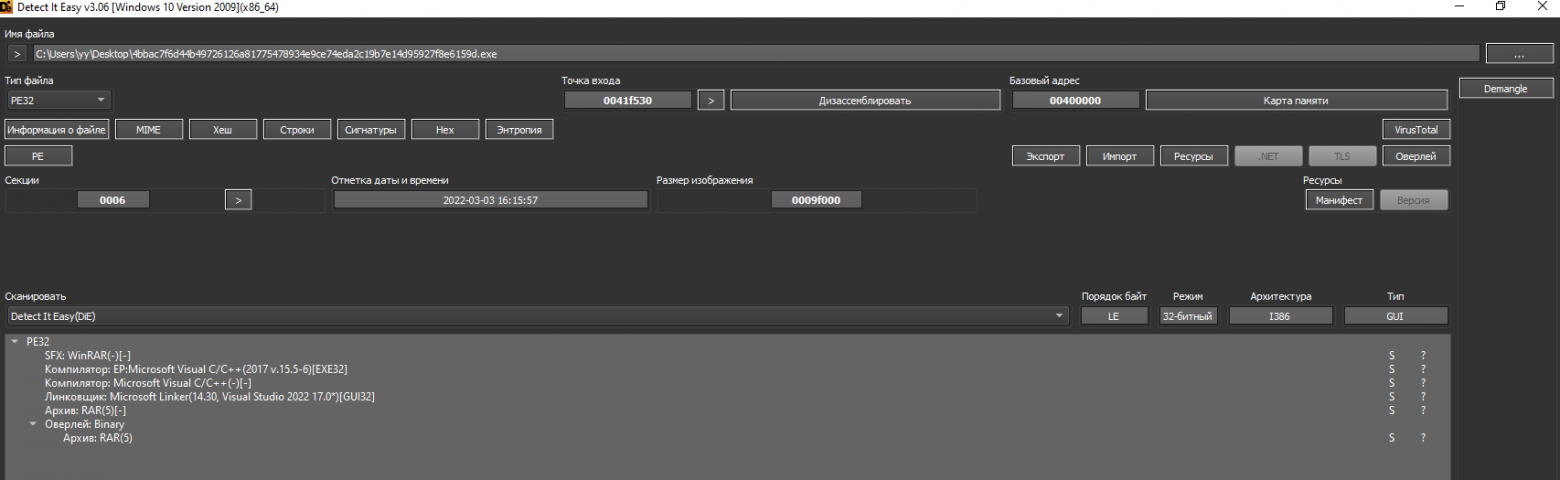
First, it is worth noting that the malware creates an unknown child process by calling rtlCreateUserProcessParametersEx, then it decodes something from Unicode and by calling NtAllocateVirtualMemory allocates a section of memory where it writes something. The process is very similar to the one that we could already observe when analyzing the Magniber ransomware.
But all of a sudden, tracing was stopped because a process was created that Tiny couldn't trace, and I get the following error:

I do not know if this can be inserted into an article, but here is an example of live analytics. Everything is fair and uncut.
Well, since we have determined that the malware introduces some kind of shellcode and interrupts the main sample, I suggest that you first deal with it, and then go through the classical statistical analysis.
This was not the end of it, the attack on PyPI gave rise to a new meta among the attackers, and this time the public NPM repository was affected.

NPM is a standard package manager that is automatically installed along with Node.js. It is used to download packages from the npm cloud server, or to upload packages to these servers.
However, the methodology of this campaign is slightly different from what we saw earlier: no one uploaded viruses directly to NPM, attackers took advantage of the high reputation of open source sources in search engines and promoted malicious sites, as well as utilities with malicious stuffing through this repository.
There are several vectors of attacks using NPM:
- The attacker creates his own website, where he places supposedly cracked applications for every taste, of course, they contain a variety of malware. Next, it uploads several hundred empty packages to NPM that contain only the file. Readme.md. This file consists of a link to the villain's website. I mentioned earlier that open source sources are well indexed by search engines, so these packages with a regular link inherit a good reputation and move up in search engines. This is so-called SEO Poisoning.
- The second option is a bit simpler and is based on the same method with the Readme file, but this time the attacker leaves a link to a fraudulent telegram channel, where he allegedly provides programs for configuring video cards for mining. This company was mainly focused on Russian users.
- Natural DoS attacks. No, you weren't imagining it. First, due to the growth in the number of packages and, as a result, an increase in traffic to the NPM site, a denial of service was caused. You can also consider the method when an attacker creates thousands of packets with a link to some victim resource, and then it is not difficult to guess what can happen, but this is only in theory and, most likely, very ineffective (but the site of an average school will not survive).
A DoS attack is a hacker attack on a computer system in order to bring it to failure, that is, creating conditions under which bona fide users of the system will not be able to access the provided system resources (servers), or this access will be difficult.
According to a report from Checkmarx, several hackers may be behind this campaign and their ultimate goal is to spread malware such as RedLine Stealer (80%), Glupteba (12%), Smoke Loader (5%) and XMRig (2%).
Redline is particularly dangerous due to a sharp increase in the number of infections, so today we will analyze and analyze it.
ReadLine Stealer: A quick overview
So, ReadLine Stealer is malware that is currently being sold on closed forums. Stiller is used by various attackers to steal data and upload other viruses to the victim's device. The exact date of its appearance is unknown, but the first malicious sample of the Redline appeared on VirusTotal in March 2020.RedLine Stealer can steal the following information: usernames, passwords, autofill data, cookies, and credit card information from all web browsers. Cybercriminals can misuse this information to access various accounts (for example, social networks, email, bank accounts, cryptocurrency wallets).
The list of e-wallets targeted by the RedLine hijacker includes Armory, AtomicWallet, BitcoinCore, Bytecoin, DashCore, Electrum, Ethereum, LitecoinCore, Monero, Exodus, Zcash, and Jaxx. The target VPN clients are ProtonVPN, OpenVPN, and NordVPN.
For analysis, we will use a sample dated April 14, 2023. On VirusTotal, it looks like this:
As you can see, there are no problems with detection here, which is good news. The external sample has an IPTV application icon and is presented as an SFX archive, but there is no other information. Let's move on to the analysis.
ReadLine Stealer: A brief statistical analysis
According to the classics, I present a setup of utilities for this article:- DIE-Detect it Easy: a multi-functional tool that has a huge arsenal. It will allow us to get ahead of the malware compiler type, language, libraries, and import/export tables with subsequent disassembly.
- PE Bear is a good tool for viewing and editing the components of a PE file.
- Tiny Tracer is a utility for dynamically tracking the execution of binary elements. The so-called tracer.
- IDA PRO is a tool for reverse engineering.
- Reko is a decompiler that is also familiar to us from previous articles.
- HollowHunter is a utility that detects and resets a lot of potentially malicious implants (replaced / implanted pes, shellcodes, interceptors, in-memory patches).
And as mentioned earlier, this is our SFX archive. I would not say that this method of packaging malware is something new and revolutionary. Similarly, in my school years, I packaged a variety of BAT files to make them look like executable. exe files.
A self-extracting or self-extracting archive (SFX) is a file or computer program that combines an archive and executable code for unpacking it. Such archives, unlike regular ones, do not require a separate program to unpack them, if the executable code can be executed in the specified operating system.
In principle, if it were launched now, the content would end up in the AppData folder, where a normal user would hardly find it. But we'll make things a little easier by simply opening .sfx using the archiver. Let's extract the file we are interested in and start parsing it.
IPTV.exe — this is the name of the extracted file, but it is much more interesting that even when viewing the properties, we can get some useful information, namely:
Approximate time of last modification, which is unlikely to be replaced, and the original file name — implossions.exe. When we try to search for this name through the search engine, we immediately see that it belongs to our stiller. The resulting sample weighs 95 KB. Let's go back to DIE for more information about the writing language and compiler of this miracle.
The exact date of creation is unknown, what we see is "Timestomping", and it is an anti-criminalistic method used to mislead the investigation and rapid response specialists.
We also see that the malware is a library .NET, and Microsoft Linker was used as the compiler.
Libraries .NET — in essence, they are the end result of compiling code in C#. Fortunately, we can easily decompile this sample using the dnSpy utility and analyze the clean source code, or at least something close to it. But if I were you, I wouldn't be happy about this, since such accessibility of the code can provoke the appearance of modifications from other attackers, and this already smacks of a full-fledged epidemic.
But first, let's use Tiny Tracer with advanced settings to clearly see what functions stiller uses. This will also display the malware's action plan.
First, it is worth noting that the malware creates an unknown child process by calling rtlCreateUserProcessParametersEx, then it decodes something from Unicode and by calling NtAllocateVirtualMemory allocates a section of memory where it writes something. The process is very similar to the one that we could already observe when analyzing the Magniber ransomware.
But all of a sudden, tracing was stopped because a process was created that Tiny couldn't trace, and I get the following error:

I do not know if this can be inserted into an article, but here is an example of live analytics. Everything is fair and uncut.
Well, since we have determined that the malware introduces some kind of shellcode and interrupts the main sample, I suggest that you first deal with it, and then go through the classical statistical analysis.