- Thread Author
- #1
Hackers are once again abusing LinkedIn Smart Links in phishing attacks to bypass protection measures and evade detection in attempts to steal Microsoft account credentials.
Smart Links are part of LinkedIn's Sales Navigator service, used for marketing and tracking, allowing Business accounts to email content using trackable links to determine who engaged with it.
Also, because Smart Link uses LinkedIn's domain followed by an eight-character code parameter, they appear to originate from a trustworthy source and bypass email protections.
The abuse of LinkedIn's Smart Link feature isn't novel, as cybersecurity firm Cofense discovered the technique in a late 2022 campaign targeting Slovakian users with bogus postal service lures.
New campaign targets Microsoft accounts
The email security company today reports it identified a surge in LinkedIn Smart Link abuse recently, with over 800 emails of various subjects leading a broad range of targets to phishing pages.
According to Cofense, the recent attacks occurred between July and August 2023, using 80 unique Smart Links, and originated from newly created or compromised LinkedIn business accounts.
Cofense data shows that the most targeted sectors of this latest campaign are finance, manufacturing, energy, construction, and healthcare.
"Despite Finance and Manufacturing having higher volumes, it can be concluded that this campaign was not a direct attack on any one business or sector but a blanket attack to collect as many credentials as possible using LinkedIn business accounts and Smart Links to carry out the attack," explains Cofense.
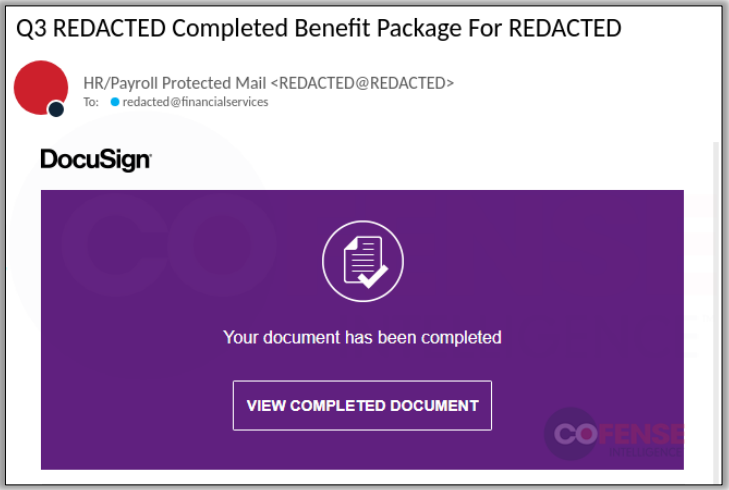
The emails sent to targets use subjects relating to payments, human resources, documents, security notifications, and others, with the embedded link/button triggering a series of redirects from a "trustworthy" LinkedIn Smart Link.
To add legitimacy to the phishing process and create a false sense of authenticity on the Microsoft login page, the Smart Link sent to victims is adjusted to contain the target's email address.
The phishing page will read the email address from the link clicked by the victim and auto-fill it on the form, only expecting the victim to fill out the password, just like it happens on the legitimate login portal.
The phishing page resembles a standard Microsoft login portal instead of a customized, company-specific design.
While this broadens its target range, it may deter individuals familiar with their employer's unique portals.
Users should be educated not to rely solely on email security tools to block threats, as phishing actors increasingly adopt tactics that abuse legitimate services to bypass these protections.
Smart Links are part of LinkedIn's Sales Navigator service, used for marketing and tracking, allowing Business accounts to email content using trackable links to determine who engaged with it.
Also, because Smart Link uses LinkedIn's domain followed by an eight-character code parameter, they appear to originate from a trustworthy source and bypass email protections.
The abuse of LinkedIn's Smart Link feature isn't novel, as cybersecurity firm Cofense discovered the technique in a late 2022 campaign targeting Slovakian users with bogus postal service lures.
New campaign targets Microsoft accounts
The email security company today reports it identified a surge in LinkedIn Smart Link abuse recently, with over 800 emails of various subjects leading a broad range of targets to phishing pages.
According to Cofense, the recent attacks occurred between July and August 2023, using 80 unique Smart Links, and originated from newly created or compromised LinkedIn business accounts.
Cofense data shows that the most targeted sectors of this latest campaign are finance, manufacturing, energy, construction, and healthcare.
You do not have permission to view link
Log in or register now.
| Targeted sectors |
The emails sent to targets use subjects relating to payments, human resources, documents, security notifications, and others, with the embedded link/button triggering a series of redirects from a "trustworthy" LinkedIn Smart Link.
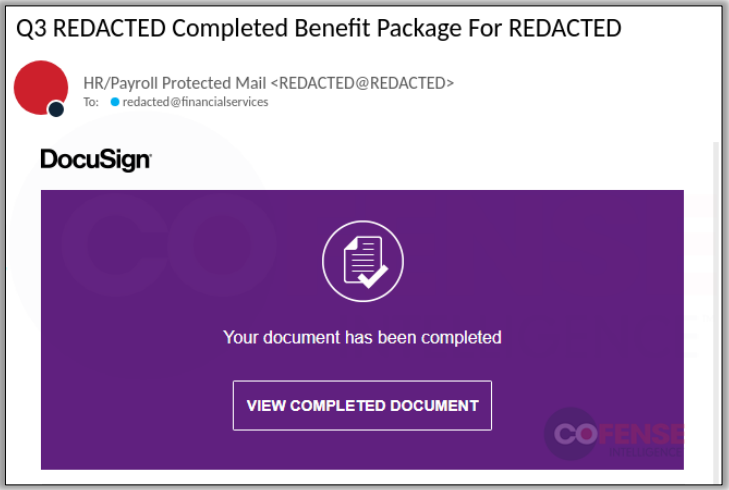
| Phishing email |
You do not have permission to view link
Log in or register now.
| Smart Link's structure |
You do not have permission to view link
Log in or register now.
| Generic Microsoft account phishing page |
While this broadens its target range, it may deter individuals familiar with their employer's unique portals.
Users should be educated not to rely solely on email security tools to block threats, as phishing actors increasingly adopt tactics that abuse legitimate services to bypass these protections.