Member
- Joined
- Oct 11, 2023
- Messages
- 105
- Thread Author
- #1
There are times when you need to make someone happy. It happens when the target organization has a second authentication factor configured — sms, Google authenticator, or Duo. What should I do in such cases? Hire gopniks? Cut employees ' phone numbers? No! It turns out that cunning hackers have written software that can help in this difficult situation.
How does it work? The author of the software
In the same article, I will talk about my experience and the pitfalls that I encountered.

enter the necessary settings. Specify the main domain (not a subdomain) and its IP address.
Code:
config domain <phishing domain>. com
config ip 10.0.0.1
As a result, the config looks like this:
Interesting parameter here redirect_url
- it indicates where to redirect the request when the client came to the root of our domain. Why is this done? If you send a phishing page from the root, the domain will be calculated very quickly and added to the lists of dangerous sites, browsers will swear threateningly, and users will never get to us. Therefore, we will send it via a unique link, and the root will redirect to the song Never Gonna Give You Up.
Fill in the description, specify the phishlet name, authors, and the required version of Evilginx.
Code:
name: 'okta'
author: '@ml_siegel, updated by @hollow1'
min_ver: '2.2.0'
We specify which domain we are going to phish. In our case, we use a domain like<имя целевой компании>.okta.com
Code:
proxy_hosts:
- {phish_sub:", orig_sub: '<target company name subdomain>', domain: 'okta.com', session: true, is_landing: true}
Parameter session
indicates that it is this domain that sends the cookies we need and that credentials are passed there,is_landing
this means that this host will be used to generate phishing URLs.
The next important step is to identify all requests to the target domain so that the proxy can successfully rewrite them to the phishing domain. If this is not done, the user will send data not to us, but directly to the original domain, and we will not catch any accounts. You only need to rewrite requests that are directly involved in the user's login process.
To clearly understand what exactly is required for successful authentication, you need to carefully study this very process. Armed with Burp and a test account, we start looking for how the password is transmitted and what cookies the application uses to determine the authorized user. We are also looking for responses from the server that contain links to the original domain.
We find a request that passes your username and password. We see that it is sent to the original domain, but we need it to go to us.

Here you can see how the original domain returns links inside javascript. They need to be rewritten.

You do not have permission to view link
Log in or register now.
is a phishing framework that acts as a proxy between the victim and the site we want to get accounts from. Previously, it used custom nginx, but now it is completely rewritten in Go. It includes mini HTTP and DNS servers, which greatly facilitates installation and deployment.How does it work? The author of the software
You do not have permission to view link
Log in or register now.
on its website, details on installation and configuration can be found on the
You do not have permission to view link
Log in or register now.
page. Why is it possible to bypass the second factor? The trick is that we do not interfere with the process of entering the code from sms / temporary password / push from DUO. We quietly wait for the user to successfully complete all the authentication steps, catch their cookie, and then use it to log in. Along the way, just in case, we collect his username and password.In the same article, I will talk about my experience and the pitfalls that I encountered.
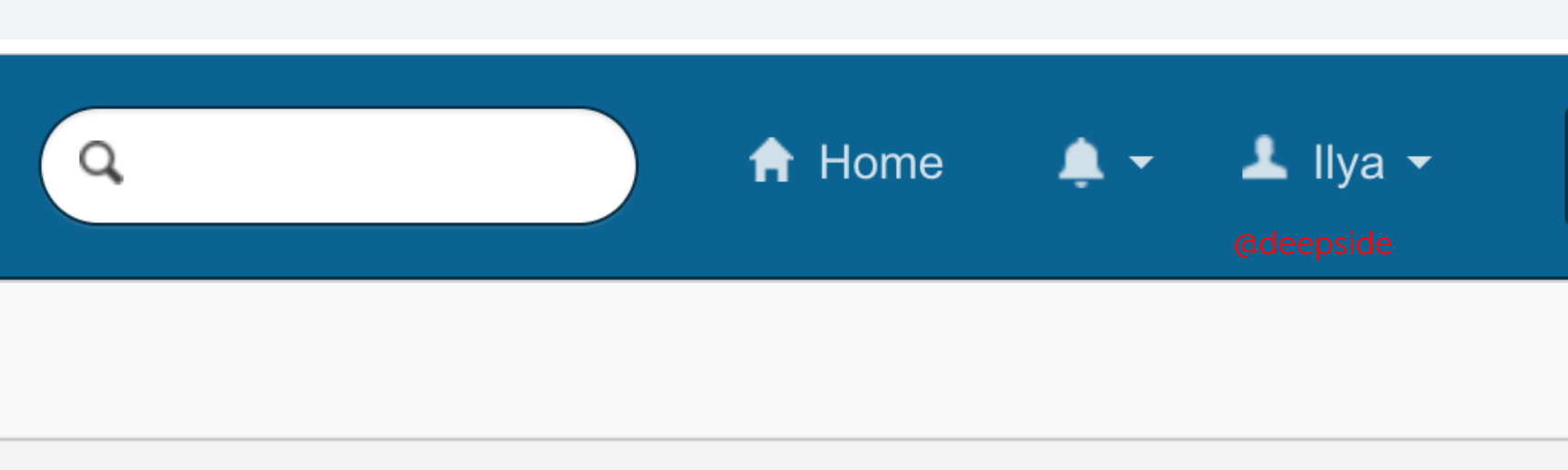
Task
So, we need to sign up an office that actively uses
You do not have permission to view link
Log in or register now.
as a Single Sign-on. As the second factor, a
You do not have permission to view link
Log in or register now.
solution is used, the feature of which is in the mobile client, which allows you to confirm the second factor through regular push notifications instead of entering 35-digit codes (hello Google Authenticator). Let's get started.Step one: register a phishing domain
In the panel of our provider, specify the address of the server where the phishing will be located. We also register a subdomain of the formokta.<фишинговый домен>.com
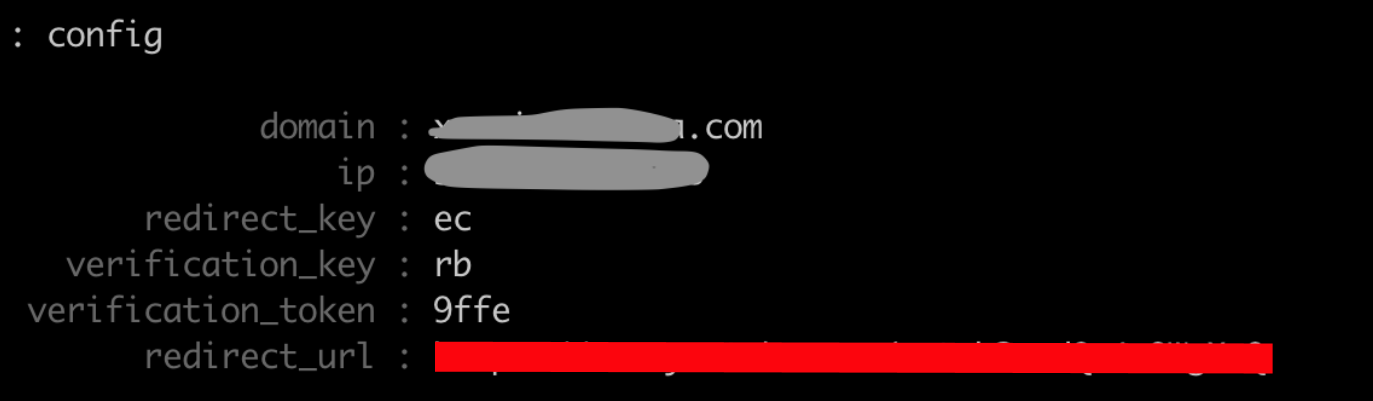
Step two-configuring Evilginx
Running Evilginx and using the commandconfigenter the necessary settings. Specify the main domain (not a subdomain) and its IP address.
Code:
config domain <phishing domain>. com
config ip 10.0.0.1
As a result, the config looks like this:
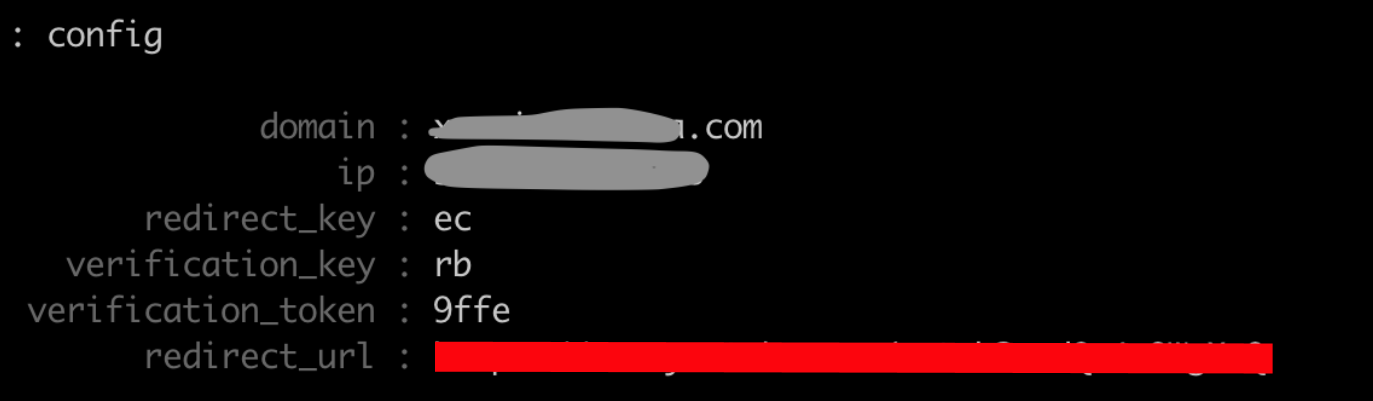
Interesting parameter here redirect_url
- it indicates where to redirect the request when the client came to the root of our domain. Why is this done? If you send a phishing page from the root, the domain will be calculated very quickly and added to the lists of dangerous sites, browsers will swear threateningly, and users will never get to us. Therefore, we will send it via a unique link, and the root will redirect to the song Never Gonna Give You Up.
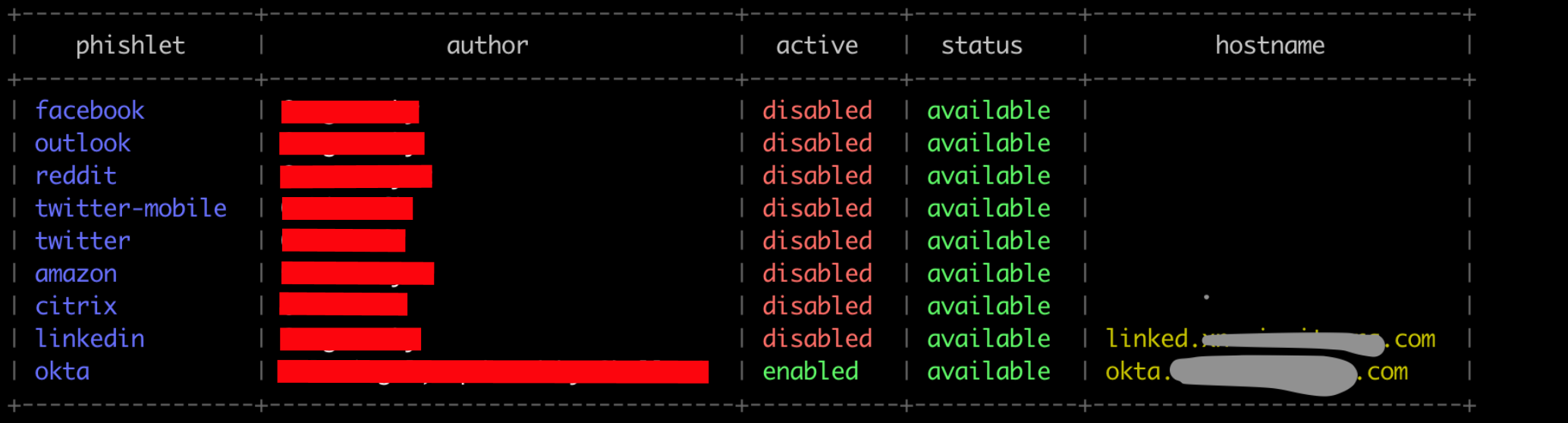
Step three-setting up a phishing page
This is where the fun begins. Since we don't actually host any content on our server at all, but only proxy requests, we need to "tell" Evilginx exactly what data we want to get. We write this "story" in a special format. Documentation on it is available on the project's
You do not have permission to view link
Log in or register now.
page. These descriptions are called phishlets. For some popular services — facebook, linkedin, amazon-they are already written and included in the distribution. We were less lucky, Okta is not supported out of the box, but good people wrote phishlet for the
You do not have permission to view link
Log in or register now.
version. We take a file and start soldering.Fill in the description, specify the phishlet name, authors, and the required version of Evilginx.
Code:
name: 'okta'
author: '@ml_siegel, updated by @hollow1'
min_ver: '2.2.0'
We specify which domain we are going to phish. In our case, we use a domain like<имя целевой компании>.okta.com
Code:
proxy_hosts:
- {phish_sub:", orig_sub: '<target company name subdomain>', domain: 'okta.com', session: true, is_landing: true}
Parameter session
indicates that it is this domain that sends the cookies we need and that credentials are passed there,is_landing
this means that this host will be used to generate phishing URLs.
The next important step is to identify all requests to the target domain so that the proxy can successfully rewrite them to the phishing domain. If this is not done, the user will send data not to us, but directly to the original domain, and we will not catch any accounts. You only need to rewrite requests that are directly involved in the user's login process.
To clearly understand what exactly is required for successful authentication, you need to carefully study this very process. Armed with Burp and a test account, we start looking for how the password is transmitted and what cookies the application uses to determine the authorized user. We are also looking for responses from the server that contain links to the original domain.
We find a request that passes your username and password. We see that it is sent to the original domain, but we need it to go to us.

Here you can see how the original domain returns links inside javascript. They need to be rewritten.